
If you have ever received a message from a phone number of a business or a person that you may know, you may trust the number that is messaging you. However, it is important to be alert of scammers who may be pretending to be a person or business you know. This fraud, known as spoofing—you may have heard the phrase before—occurs when a caller tries to conceal their identity by purposely falsifying the information supplied to your caller ID display.
What is spoofing?
To elaborate, you probably receive spoof calls frequently. They come from a single source that hides its phone number as a different one. Scammers are simply spoofing those digits to get you to pick up the phone, where they may use numbers having your area code or belonging to well-known companies. However, it is important to note that con artists are now appearing through text messages of numbers you may recognize. While this is not a new way to scam, it is becoming more prominent as well as more advanced to trick users in believing the text is legitimate. More shockingly than this, it is important to note that anyone can spoof a phone number, including you.
Nowadays, spoofing is more complex and targeted than ever.
Text Magic states, “SMS spoofing is changing sender details like a phone number and/or contact name and can be used for fraudulent purposes” (Text Magic). Some of the ways that SMS can be illegally used is by a user posing as a company, fake money transfers, spoofing to gain personal information, and having a personal agenda.
Recently, a user received a text message from her bank's general phone number that she had saved in her contacts informing her that her banking account had been stolen. Ultimately, she recognized the number since her bank had previously used it to send her messages. However, she thought the nature of the message was amateurish. Later, after calling her bank through customer service, she realized that the user was a scammer attempting to steal her personal information.
Scammers aren’t only using big companies' phone numbers to send spoof messages. In fact, scammers can use any number that they can find. The other day, a user missed an unknown call that they later returned. The caller stated that the user had messaged them asking for his personal information. The user never called anyone to ask for their information. Furthermore, scammers are messaging customers and companies in an effort to defraud. A breach or even clicking on a malicious link from one of your devices could lead to scammers using your number.
Phone Spoofing Services
As previously mentioned, anyone can falsify a phone number. You can imitate another caller using a variety of online services, however many of them aren't free. One popular service is Spoof Card, which only requires that you enter your real phone number and generate a PIN code. After completing this, you will have access to an account where you can select any phone number you like.
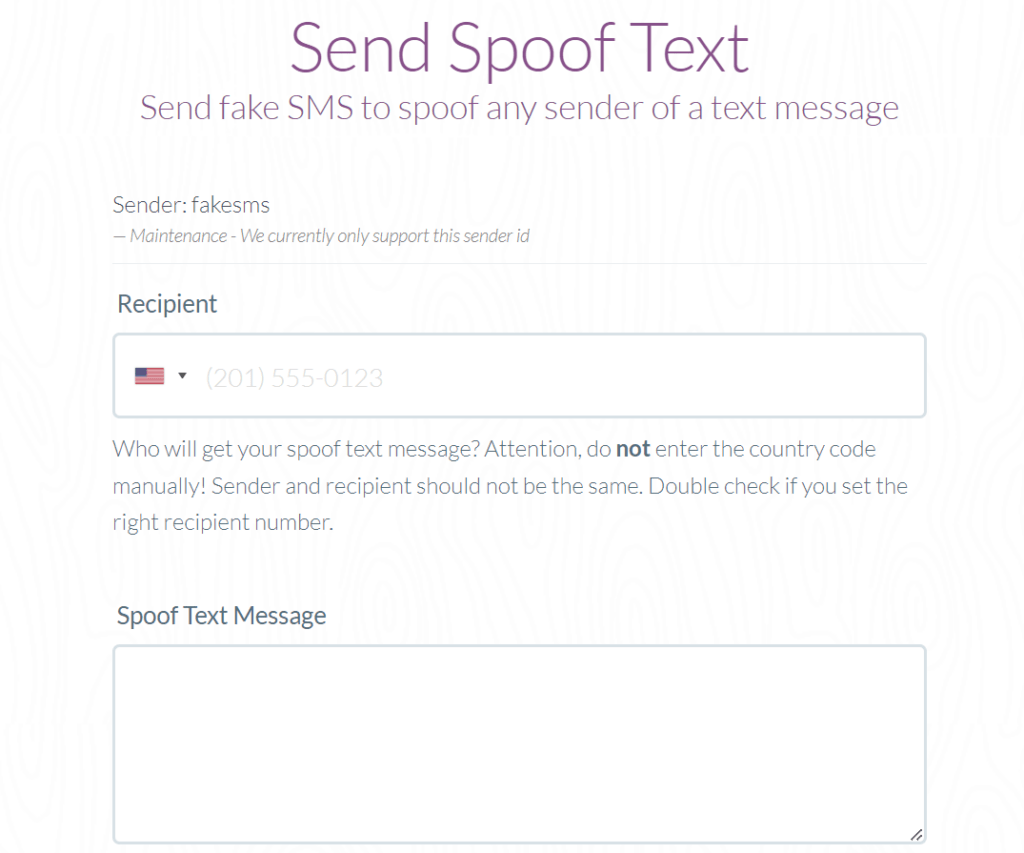
There is also a service called Spoof Box where a user can send fake SMS to spoof any sender of a text message. All you must do is type in your recipient’s phone number, type out your desired text message, and the date and time you would like the message to be sent. Just like that, one can imitate another user.
What Can I Do to Avoid Spoofing Messages?
When it comes to staying alert of a spoofing message, you should do the following:
- Examine the sender's specifics, such as the message's grammar
- Avoid clicking on unfamiliar links
- Avoid anyone asking for your personal information
- Avoid ‘too good to be true’ text messages
- Only share your phone number in important cases
If you want to be 100% confident about the message you received, look up the contact information of the institution that the sender is claiming to be, and contact them to verify if they reached out to you.
Overall, make sure that you are alert when receiving text messages. Double checking the sender and doing thorough research can save you the issues of your personal information being stolen or being scammed.
The Infiniwiz technical team in the Chicagoland area takes a proactive approach to your cybersecurity. We set up the right IT protocols and help you put in place the employee procedures that will keep your data and network safe from online hackers. However, make sure to do your part in staying alert. If you have any questions, feel free to contact us!




